Repeaters
The repeaters take the signal they receive from the network devices and regenerate it to keep it intact during its transmission through the physical environment. Since all components of the physical environment of a network (copper, fiber optic cables and wireless media) have to control the attenuation that limits the possible distance between the different nodes of the network, repeaters are an excellent way to extend the net physically.
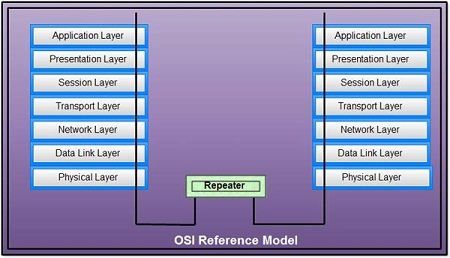
When an electrical signal travels along a medium it gets attenuated depending upon the medium characteristics. That is why a LAN cannot send signal beyond a certain limit imposed by the different types of LAN technologies. To increase the length of the LAN, repeaters are frequently used. Repeaters in its simplest form relay analog electric signal. It means that they transmit the physical layer signals or data and therefore correspond to the bottom layer of OSI model.
Repeater amplifies the signal, which has got attenuated during the course of transmission because of the physical conditions imposed by the transmission media. It also restores the signal to its original shape. The specific characteristic of repeater is that whatever it receives it transmits to the other LAN segment. This does not understand the frame format and also physical addresses. In other words, it is a transparent device. Therefore, multiple LANs connected by repeaters may be considered as a single LAN.
Since repeaters are devices that operate in the physical layer, they do not examine the data packets they receive, nor do they know any of the logical or physical addresses related to those packets. It means that the location of a repeater hardly affects the transmission speed of the information flow in the network. The repeater is limited to expanding the data signals received from a particular segment of the network and passing them to another segment of the network, as the data moves to its final destination.
The repeaters extend the data signal from one segment of the network and pass it to another segment of the network, thus expanding the size of the network.
Repeaters are also often called concentrates. Hubs that have the same functions as repeaters to amplify the signal are known as active hubs or multi-port repeaters. All these devices (regardless of the term used to designate them) operate in the physical layer of the OSI model.
Classification of Repeaters
Repeaters can be classified into two categories. These are local and remote repeaters. Local repeaters are used to connect LAN segments separated by a very small distance.
Remote repeaters are used to connect LAN segments that are far from each other. A transmission line known as a link segment is provided between two remote repeaters. No nodes can be connected to this line
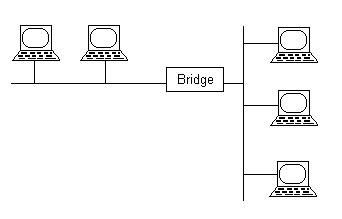
Bridges
A bridge is one of the network devices in computer networks to connect two or more communication networks or network segments and creates a single network. It provides interconnection with other computer networks, which use the same protocol. The multiple local area networks (LANs) can be connected to form a larger local area network.
In simple words, a bridge in computer networks is defined as, the network device that provides a connection between two local area networks (LANs) or two segments of the same local area network. It is also known as an adobe bridge or network bridging. It operates under the data link layer of the OSI model, hence referred to as layer 2 switches.
Types of Bridges in Computer Network
The following are the 3 types of bridges on computer networks discussed below.
Transparent Type
This type of bridge is not visible to other stations or devices on the network. It is not to reconfigure the station because the bridge is either added or deleted from the network. The function of the transparent bridge is to block or forward the data packet based on the MAC address. It is the most popular type of bridge used in computer networks.
Translational Type
this type of bridge is used to convert one networking system to another. That means it translates the received data. For example, two different networks such as the token ring network and the Ethernet network can be connected using the translational bridge. Depending on the direction, it can remove or add the fields and information from the frame when needed.
Source-route Type
This type of bridge is designed by IBM for the token ring networks. The entire route of the frame is embedded within the frame and the routing operation is performed by the source station to forward the frame and follow the specific route. The special frame discovered by the host is called as discovery frame. It spreads over the whole network and uses all the paths possible to reach the destination.
Uses of Bridge in Computer Network
In computer networks, the bridges are used to connect multiple local area networks with the same protocol and achieve communication between the components or devices, or nodes connected to the network. The use of the bridge in a computer network is explained below.
- When the multiple local area networks are joined together to form a single local area network using the bridge, the capacity of the network is multiplied and increased.
- When the data frame is received, the database in the bridge helps to decide whether to transmit or discard the data frame.
- The function of the bridge takes place in the data link layer of the OSI model to transmit the data frames to the multiple nodes in the network.
- The data frame is passed and discarded by the bridge only when the data frame contains the MAC address or destination address.
- Similarly, the data frame is forwarded towards it only when the frame contains a MAC address in the network, which is connected.
- A single faulty node is prevented from the network by forwarding or discarding the frame.
- Helps to broadcast the frames to every node even if the MAC address or destination address is not available.
- The wireless networks with wireless segments can be connected using a wireless bridge.
Functions of Bridges in the Network
The bridge in a computer network is used to block or forward the data based on the MAC address of the destination, which is written into each frame of data. When the destination address is on a network, the bridge helps in forwarding the data to the other connected networks. If there is no address, then it blocks the data from passing.
- The functions of the bridge in the network are given below.
- The bridges in networks are used to divide the local area network (LAN) into various segments.
- These works on the OSI model under the data link layer
- These are used to store the MAC address of computers in the network
- These are used to reduce the traffic in the network.
- These are used to filter the content by using the MAC address of the source and destination.
- Used for interconnecting two LANs using the single and same protocol
- Multiple virtual LANs can be connected to form a single larger LAN
- A bridge can switch to any type of data packets such as Apple talk packets or IP packets above the network layer because the payload field of the data frame is not considered. Only the MAC address or destination address of the frame is considered to block or forward the data to the nodes in the network.
Advantages/Disadvantages
Bridges are the network devices that are used to interconnect two or more computer networks together and divide the LAN into multiple segments. These don’t broadcast traffic effectively but manages to broadcast the traffic to the segments of the network. The advantages/disadvantages of the bridge in a computer network are discussed below
The advantages of the bridge in the computer network include the following.
- Extension of the Network: The bridges are used as a repeater to extend the network. That means thee networks with different topologies can be connected
- Increases Bandwidth: Separate collision domain is shared by some of the individual nodes present on the network, which results in increased bandwidth.
- The reliability of the network is high to maintain the network easily. The traffic on the network can be reduced by dividing the local area network into several segments.
- When the different MAC protocols are used for different segments, frame buffering is created.
- The transparency of protocol is at a higher level because the bridges function at the MAC layer.
- No special hardware or software or architecture is required to install the bridge in the network to provide functional support because they should be transparent.
The disadvantages of the bridge in the computer network include the following.
- The cost of the bridges is more when compared to hubs and repeaters. It is mainly used only in the network traffic load of the LAN. While in variable data load, either hub or repeater is used.
- The speed of the network is slow when compared to the repeater due to the frame buffering and relays.
- The potential performance of the network is poor because additional processing is required to view the MAC address of the frame on the network.
Gateways
A gateway is a network node used in telecommunications that connects two networks with different transmission protocols together. Gateways serve as an entry and exit point for a network as all data must pass through or communicate with the gateway prior to being routed. In most IP-based networks, the only traffic that does not go through at least one gateway is traffic flowing among nodes on the same local area network (LAN) segment. The term default gateway or network gateway may also be used to describe the same concept.
The primary advantage of using a gateway in personal or enterprise scenarios is simplifying internet connectivity into one device. In the enterprise, a gateway node can also act as a proxy server and a firewall. Gateways can be purchased through popular technology retailers, such as Best Buy, or rented through an internet service provider.
How gateways work
All networks have a boundary that limits communication to devices that are directly connected to it. Due to this, if a network wants to communicate with devices, nodes or networks outside of that boundary, they require the functionality of a gateway. A gateway is often characterized as being the combination of a router and a modem.
The gateway is implemented at the edge of a network and manages all data that is directed internally or externally from that network. When one network wants to communicate with another, the data packet is passed to the gateway and then routed to the destination through the most efficient path. In addition to routing data, a gateway will also store information about the host network’s internal paths and the paths of any additional networks that are encountered.
Gateways are basically protocol converters, facilitating compatibility between two protocols and operating on any layer of the open systems interconnection (OSI) model.
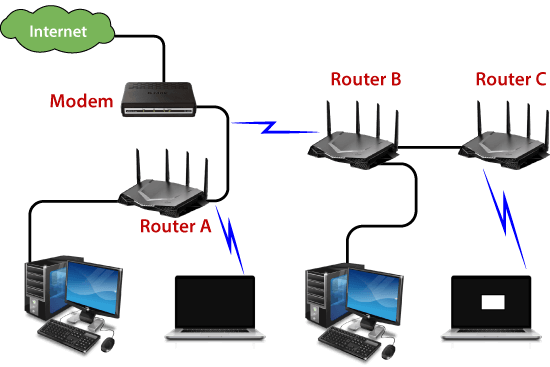
Routers
The router is a physical or virtual internetworking device that is designed to receive, analyze, and forward data packets between computer networks. A router examines a destination IP address of a given data packet, and it uses the headers and forwarding tables to decide the best way to transfer the packets. There are some popular companies that develop routers; such are Cisco, 3Com, HP, Juniper, D-Link, Nortel, etc. Some important points of routers are given below:
- A router is used in LAN (Local Area Network) and WAN (Wide Area Network) environments. For example, it is used in offices for connectivity, and you can also establish the connection between distant networks such as from Bhopal to
- It shares information with other routers in networking.
- It uses the routing protocol to transfer the data across a network.
- Furthermore, it is more expensive than other networking devices like switches and hubs.

A router works on the third layer of the OSI model, and it is based on the IP address of a computer. It uses protocols such as ICMP to communicate between two or more networks. It is also known as an intelligent device as it can calculate the best route to pass the network packets from source to the destination automatically.
A virtual router is a software function or software-based framework that performs the same functions as a physical router. It may be used to increase the reliability of the network by virtual router redundancy protocol, which is done by configuring a virtual router as a default gateway. A virtual router runs on commodity servers, and it is packaged with alone or other network functions, like load balancing, firewall packet filtering, and wide area network optimization capabilities.
How does Router work?
A router analyzes a destination IP address of a given packet header and compares it with the routing table to decide the packet’s next path. The list of routing tables provides directions to transfer the data to a particular network destination. They have a set of rules that compute the best path to forward the data to the given IP address.
Routers use a modem such as a cable, fiber, or DSL modem to allow communication between other devices and the internet. Most of the routers have several ports to connect different devices to the internet at the same time. It uses the routing tables to determine where to send data and from where the traffic is coming.
A routing table mainly defines the default path used by the router. So, it may fail to find the best way to forward the data for a given packet. For example, the office router along a single default path instructs all networks to its internet services provider.
There are two types of tables in the router that are static and dynamic. The static routing tables are configured manually, and the dynamic routing tables are updated automatically by dynamic routers based on network activity.
Features of Router
- A router works on the 3rd layer (Network Layer) of the OSI model, and it is able to communicate with its adjacent devices with the help of IP addresses and subnet.
- A router provides high-speed internet connectivity with the different types of ports like gigabit, fast-Ethernet, and STM link port.
- It allows the users to configure the port as per their requirements in the network.
- Routers’ main components are central processing unit (CPU), flash memory, RAM, Non-Volatile RAM, console, network, and interface card.
- Routers are capable of routing the traffic in a large networking system by considering the sub-network as an intact network.
- Routers filter out the unwanted interference, as well as carry out the data encapsulation and decapsulation process.
- Routers provide the redundancy as it always works in master and slave mode.
- It allows the users to connect several LAN and WAN.
- Furthermore, a router creates various paths to forward the data.
Applications of Routers
There are various areas where a router is used:
- Routers are used to connect hardware equipment with remote location networks like BSC, MGW, IN, SGSN, and other servers.
- It provides support for a fast rate of data transmission because it uses high STM links for connectivity; that’s why it is used in both wired or wireless communication.
- Internet service providers widely use routers to send the data from source to destination in the form of e-mail, a web page, image, voice, or a video file. Furthermore, it can send data all over the world with the help of an IP address of the destination.
- Routers offer access restrictions. It can be configured in a way that allows for few users to access the overall data and allows others to access the few data only, which is defined for them.
- Routers are also used by software testers for WAN communications. For example, the software manager of an organization is located in Agra, and its executive is located at a different place like Pune or Bangalore. Then the router provides the executive the method to share his software tools and other applications with the manager with the help of routers by connecting their PCs to the router using WAN architecture.
Types of Routers
There are various types of routers in networking; such are given below:
1. Wireless Router: Wireless routers are used to offer Wi-Fi connectivity to laptops, smartphones, and other devices with Wi-Fi network capabilities, and it can also provide standard ethernet routing for a small number of wired network systems.
Wireless routers are capable of generating a wireless signal in your home or office, and it allows the computers to connect with routers within a range, and use the internet. If the connection is indoors, the range of the wireless router is about 150 feet, and when the connection is outdoors, then its range is up to 300 feet.
Furthermore, you can make more secure wireless routers with a password or get your IP address. Thereafter, you can log in to your router by using a user ID and password that will come with your router.
2. Brouter: A brouter is a combination of the bridge and a router. It allows transferring the data between networks like a bridge. And like a router, it can also route the data within a network to the individual systems. Thus, it combines these two functions of bridge and router by routing some incoming data to the correct systems while transferring the other data to another network.
3. Core router: A core router is a type of router that can route the data within a network, but it is not able to route the data between the networks. It is a computer communication system device and the backbone of networks, as it helps to link all network devices. It is used by internet service providers (ISPs), and it also provides various types of fast and powerful data communication interfaces.
4. Edge router: An edge router is a lower-capacity device that is placed at the boundary of a network. It allows an internal network to connect with the external networks. It is also called as an access router. It uses an External BGP (Border Gateway Protocol) to provides connectivity with remote networks over the internet.
There are two types of edge routers in networking:
- Subscriber edge router
- Label edge router
The subscriber edge router belongs to an end-user organization, and it works in a situation where it acts on a border device.
The label edge router is used in the boundary of Multiprotocol Label Switching (MPLS) networks. It acts as a gateway between the LAN, WAN, or the internet.
5. Broadband routers: Broadband routers are mainly used to provide high-speed internet access to computers. It is needed when you connect to the internet through phone and use voice over IP technology (VOIP).
All broadband routers have the option of three or four Ethernet ports for connecting the laptop and desktop systems. A broadband router is configured and provided by the internet service provider (ISP). It is also known as a broadband modem, asymmetric digital subscriber line (ADSL), or digital subscriber line (DSL) modem.
Benefits of Router
There are so many benefits of a router, which are given below:
- Security: Router provides the security, as LANs work in broadcast mode. The information is transmitted over the network and traverses the entire cable system. Although the data is available to each station, but the station which is specifically addressed reads the data.
- Performance enhancement: It enhances the performance within the individual network. For example, if a network has 14 workstations, and all generate approximately the same volume of traffic. The traffic of 14 workstations runs through the same cable in a single network. But if the network is divided into two sub-networks each with 7 workstations, then a load of traffic is reduced to half. As each of the networks has its own servers and hard disk, so fewer PCs will need the network cabling system.
- Reliability: Routers provide reliability. If one network gets down when the server has stopped, or there is a defect in the cable, then the router services, and other networks will not be affected. The routers separate the affected network, whereas the unaffected networks remain connected, without interrupting the work and any data loss.
- Networking Range: In networking, a cable is used to connect the devices, but its length cannot exceed 1000 meters. A router can overcome this limitation by performing the function of a repeater (Regenerating the signals). The physical range can be as per the requirement of a particular installation, as long as a router is installed before the maximum cable range exceeds.
The Neywork layer
Layer-3 in the OSI model is called Network layer. Network layer manages options pertaining to host and network addressing, managing sub-networks, and internetworking.
Network layer takes the responsibility for routing packets from source to destination within or outside a subnet. Two different subnet may have different addressing schemes or non-compatible addressing types. Same with protocols, two different subnet may be operating on different protocols which are not compatible with each other. Network layer has the responsibility to route the packets from source to destination, mapping different addressing schemes and protocols.
Layer-3 Functionalities
Devices which work on Network Layer mainly focus on routing. Routing may include various tasks aimed to achieve a single goal. These can be:
- Addressing devices and networks.
- Populating routing tables or static routes.
- Queuing incoming and outgoing data and then forwarding them according to quality of service constraints set for those packets.
- Internetworking between two different subnets.
- Delivering packets to destination with best efforts.
- Provides connection oriented and connection less mechanism.
Network Layer Features
With its standard functionalities, Layer 3 can provide various features as:
- Quality of service management
- Load balancing and link management
- Security
- Interrelation of different protocols and subnets with different schema.
- Different logical network design over the physical network design.
- L3 VPN and tunnels can be used to provide end to end dedicated connectivity.
Internet protocol is widely respected and deployed Network Layer protocol which helps to communicate end to end devices over the internet. It comes in two flavors. IPv4 which has ruled the world for decades but now is running out of address space. IPv6 is created to replace IPv4 and hopefully mitigates limitations of IPv4 too.
Design issues in network layer
Network layer is majorly focused on getting packets from the source to the destination, routing error handling and congestion control.
Before learning about design issues in the network layer, let’s learn about it’s various functions.
- Addressing:
Maintains the address at the frame header of both source and destination and performs addressing to detect various devices in network. - Packeting:
This is performed by Internet Protocol. The network layer converts the packets from its upper layer. - Routing:
It is the most important functionality. The network layer chooses the most relevant and best path for the data transmission from source to destination. - Inter-networking:
It works to deliver a logical connection across multiple devices.
Network layer design issues:
The network layer comes with some design issues they are described as follows:
1. Store and Forward packet switching:
The host sends the packet to the nearest router. This packet is stored there until it has fully arrived once the link is fully processed by verifying the checksum then it is forwarded to the next router till it reaches the destination. This mechanism is called “Store and Forward packet switching.”
2. Services provided to Transport Layer:
Through the network/transport layer interface, the network layer transfers it’s services to the transport layer. These services are described below.
But before providing these services to the transfer layer following goals must be kept in mind :-
- Offering services must not depend on router technology.
- The transport layer needs to be protected from the type, number and topology of the available router.
- The network addresses for the transport layer should use uniform numbering pattern also at LAN and WAN connections.
Based on the connections there are 2 types of services provided :
- Connectionless – The routing and insertion of packets into subnet is done individually. No added setup is required.
- Connection-Oriented – Subnet must offer reliable service and all the packets must be transmitted over a single route.
3. Implementation of Connectionless Service:
Packet are termed as “datagrams” and corresponding subnet as “datagram subnets”. When the message size that has to be transmitted is 4 times the size of the packet, then the network layer divides into 4 packets and transmits each packet to router via. a few protocol.Each data packet has destination address and is routed independently irrespective of the packets.
4. Implementation of Connection Oriented service:
To use a connection-oriented service, first we establishes a connection, use it and then release it. In connection-oriented services, the data packets are delivered to the receiver in the same order in which they have been sent by the sender.
It can be done in either two ways :
- Circuit Switched Connection – A dedicated physical path or a circuit is established between the communicating nodes and then data stream is transferred.
- Virtual Circuit Switched Connection – The data stream is transferred over a packet switched network, in such a way that it seems to the user that there is a dedicated path from the sender to the receiver. A virtual path is established here. While, other connections may also be using the same path.
What is a Routing Algorithm?
A routing algorithm is a routing protocol decided by the network layer where the data packets are transmitted from source to destination. This algorithm provides the best path i e, the least-cost path, through which data is transmitted from sender/source to receiver/destination.
A set of operations are performed by the network layer, which regulates the traffic of internet usage effectively and efficiently. This is known as a routing algorithm in computer networks. It is used to determine the best path or route mathematically.
Routing Algorithm in Computer Networks
In communication networks, there will be multiple paths to transfer the data from source to destination. One path should be preferred over others to reach the destination. The process of selecting the path or showing the path is known as routing. Routers are the network devices used to select the route by some software programming. In computer networks, it contains the information regarding the selected best routes, through which data is to be transferred from source to destination.
For example, to compute the best path, this algorithm uses different methods. One of the methods is the distance vector method. In this type of routing, all the possible routes at every node (point) are computed in the form of a graph that gives the cost of travel to the immediate node/neighbor. The total routing information will be collected to create a routing table (distance table), which is used to calculate the best route from one node to another node. An example of the routing algorithm is shown below figure.
Routing Algorithm
Different Types
There are different types of routing algorithms, to determine the best path for data packets at every to reach the receiver or destination. A routing table is created to check whether the incoming data line matches with the output data.
The different types of routing algorithm are,
- Distance-Vector Algorithm: it is required to exchange the information between the nodes, which are connected directly.
- Link State Routing Algorithm: it is also known as centralized routing.
- Path to the Vector Routing Algorithm
Types of Routing Algorithm in Computer Networks
It is a routing protocol used to show the best route, through which data packets are transmitted to the destination. It helps to transfer the data to the destination effectively. There are 2 types of routing algorithms in computer networks. They are,
Adaptive Type
It is also known as dynamic routing. The selection of routes and change of routing decisions depends on the network traffic and topology used. It calculates and optimizes parameters like hop count, the distance of the path to reach the destination, and approximate transit time. It requires dynamic data like network topology, load, and delays to select the best route.
Isolated Routing
It is a routing algorithm, which takes the information of the routing from the local information other than the information from the neighbor nodes. Routing decisions are done by using only the local information that it has and it doesn’t gather any data from other nodes. The node will not have any information regarding the status of the link. The main disadvantage of an isolated routing algorithm is, the data packets are transferred through a narrow/congested network, which results in a delay to reach the destination. Examples are hot potato routing and backward learning.
Centralized Routing
This type of algorithm is also known as global routing or link-state routing. With the help of complete information of the network topology, it calculates and selects the best least-cost route to transfer the data packets between the sender/source and receiver/destination. The connection between the nodes and input as link cost is achieved before the calculation of routes.
The centralized node contains all the data of the network topology to make correct routings and if there is any failure, then the total network goes down. The main advantage is, only one node will have the information about the total network.
Distribution Routing
This type of routing algorithm is also known as decentralized routing or distance vector routing algorithm because it calculates the least-cost route between the destination and source. The node, which sends the data packets receives the information from the neighbors and decides the routing of the data packets to reach the destination. If there is any change in the time interval while receiving the information, the sending of the data packet might be delayed.
The node, which sends the data packets doesn’t contain any information about the complete route between the source and destination and network links. It contains the information about the least-cost path, through which data packets are to be transferred
Non-adaptive Type
It is also referred to as static routing. In this type of algorithm, the routing of the data packets doesn’t depend on the network topology and the traffic of the network. The routers store the information of the routing when the network gets booted. The best route will be decided in advance and there will be no change.
Flooding Routing
In this type, all the outgoing links receive every incoming data packet except the one, from which the packet has generated. The duplicate packets might be generated at the node due to the loop links. This drawback can be resolved by using sequential numbers, spanning tree, and hop count.
Random Walk Routing
In this type of routing algorithm, the data packets are transferred between host to host or node to node to one of its neighbors reach the destination randomly. This type is very hard and the packets are transferred onto the link, which is in the queue.
Congestion control algorithm
Congestion causes choking of the communication medium. When too many packets are displayed in a method of the subnet, the subnet’s performance degrades. Hence, a network’s communication channel is called congested if packets are traversing the path and experience delays mainly over the path’s propagation delay.
There is two congestion control algorithm which is as follows:
Leaky Bucket
The leaky bucket algorithm discovers its use in the context of network traffic shaping or rate-limiting. The algorithm allows controlling the rate at which a record is injected into a network and managing burstiness in the data rate.
A leaky bucket execution and a token bucket execution are predominantly used for traffic shaping algorithms. This algorithm is used to control the rate at which traffic is sent to the network and shape the burst traffic to a steady traffic stream.
The figure shows the leaky bucket algorithm.
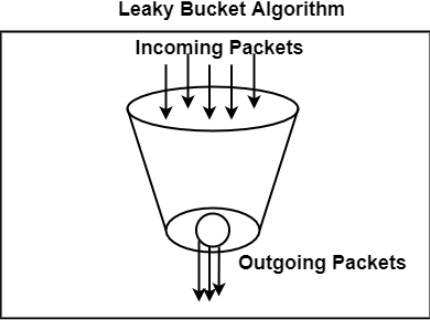
In this algorithm, a bucket with a volume of, say, b bytes and a hole in the Notes bottom is considered. If the bucket is null, it means b bytes are available as storage. A packet with a size smaller than b bytes arrives at the bucket and will forward it. If the packet’s size increases by more than b bytes, it will either be discarded or queued. It is also considered that the bucket leaks through the hole in its bottom at a constant rate of r bytes per second.
The outflow is considered constant when there is any packet in the bucket and zero when it is empty. This defines that if data flows into the bucket faster than data flows out through the hole, the bucket overflows.
The disadvantages compared with the leaky-bucket algorithm are the inefficient use of available network resources. The leak rate is a fixed parameter. In the case of the traffic, volume is deficient, the large area of network resources such as bandwidth is not being used effectively. The leaky-bucket algorithm does not allow individual flows to burst up to port speed to effectively consume network resources when there would not be resource contention in the network.
Token Bucket Algorithm
The leaky bucket algorithm has a rigid output design at the average rate independent of the bursty traffic. In some applications, when large bursts arrive, the output is allowed to speed up. This calls for a more flexible algorithm, preferably one that never loses information. Therefore, a token bucket algorithm finds its uses in network traffic shaping or rate-limiting.
It is a control algorithm that indicates when traffic should be sent. This order comes based on the display of tokens in the bucket. The bucket contains tokens. Each of the tokens defines a packet of predetermined size. Tokens in the bucket are deleted for the ability to share a packet.
When tokens are shown, a flow to transmit traffic appears in the display of tokens. No token means no flow sends its packets. Hence, a flow transfers traffic up to its peak burst rate in good tokens in the bucket.
Thus, the token bucket algorithm adds a token to the bucket each 1 / r seconds. The volume of the bucket is b tokens. When a token appears, and the bucket is complete, the token is discarded. If a packet of n bytes appears and n tokens are deleted from the bucket, the packet is forwarded to the network.
When a packet of n bytes appears but fewer than n tokens are available. No tokens are removed from the bucket in such a case, and the packet is considered non-conformant. The non-conformant packets can either be dropped or queued for subsequent transmission when sufficient tokens have accumulated in the bucket.
They can also be transmitted but marked as being non-conformant. The possibility is that they may be dropped subsequently if the network is overloaded.
Quality of service
QoS is an overall performance measure of the computer network.
Important flow characteristics of the QoS are given below:
1. Reliability
If a packet gets lost or acknowledgement is not received (at sender), the re-transmission of data will be needed. This decreases the reliability.
The importance of the reliability can differ according to the application.
For example:
E- mail and file transfer need to have a reliable transmission as compared to that of an audio conferencing.
2. Delay
Delay of a message from source to destination is a very important characteristic. However, delay can be tolerated differently by the different applications.
For example:
The time delay cannot be tolerated in audio conferencing (needs a minimum time delay), while the time delay in the e-mail or file transfer has less importance.
3. Jitter
The jitter is the variation in the packet delay.
If the difference between delays is large, then it is called as high jitter. On the contrary, if the difference between delays is small, it is known as low jitter.
Example:
Case1: If 3 packets are sent at times 0, 1, 2 and received at 10, 11, 12. Here, the delay is same for all packets and it is acceptable for the telephonic conversation.
Case2: If 3 packets 0, 1, 2 are sent and received at 31, 34, 39, so the delay is different for all packets. In this case, the time delay is not acceptable for the telephonic conversation.
4. Bandwidth
Different applications need the different bandwidth.
For example:
Video conferencing needs more bandwidth in comparison to that of sending an e-mail.
Integrated Services and Differentiated Service
These two models are designed to provide Quality of Service (QoS) in the network.
1. Integrated Services( IntServ)
Integrated service is flow-based QoS model and designed for IP.
In integrated services, user needs to create a flow in the network, from source to destination and needs to inform all routers (every router in the system implements IntServ) of the resource requirement.
Following are the steps to understand how integrated services works.
I) Resource Reservation Protocol (RSVP)
An IP is connectionless, datagram, packet-switching protocol. To implement a flow-based model, a signaling protocol is used to run over IP, which provides the signaling mechanism to make reservation (every applications need assurance to make reservation), this protocol is called as RSVP.
ii) Flow Specification
While making reservation, resource needs to define the flow specification. The flow specification has two parts:
a) Resource specification
It defines the resources that the flow needs to reserve. For example: Buffer, bandwidth, etc.
b) Traffic specification
It defines the traffic categorization of the flow.
iii) Admit or deny
After receiving the flow specification from an application, the router decides to admit or deny the service and the decision can be taken based on the previous commitments of the router and current availability of the resource.
Classification of services
The two classes of services to define Integrated Services are:
a) Guaranteed Service Class
This service guarantees that the packets arrive within a specific delivery time and not discarded, if the traffic flow maintains the traffic specification boundary.
This type of service is designed for real time traffic, which needs a guaranty of minimum end to end delay.
For example: Audio conferencing.
b) Controlled Load Service Class
This type of service is designed for the applications, which can accept some delays, but are sensitive to overload network and to the possibility to lose packets.
For example: E-mail or file transfer.
Problems with Integrated Services.
The two problems with the Integrated services are:
i) Scalability
In Integrated Services, it is necessary for each router to keep information of each flow. But, this is not always possible due to growing network.
ii) Service- Type Limitation
The integrated services model provides only two types of services, guaranteed and control-load.
2. Differentiated Services (DS or Diffserv):
- DS is a computer networking model, which is designed to achieve the scalability by managing the network traffic.
- DS is a class based QoS model specially designed for IP.
- DS was designed by IETF (Internet Engineering Task Force) to handle the problems of Integrated Services.
The solutions to handle the problems of Integrated Services are explained below:
1. Scalability
The main processing unit can be moved from central place to the edge of the network to achieve the scalability. The router does not need to store the information about the flows and the applications (or the hosts) define the type of services they want every time while sending the packets.
2. Service Type Limitation
The routers, route the packets on the basis of class of services define in the packet and not by the flow. This method is applied by defining the classes based on the requirement of the applications.
Internetworking
Internetworking is the process or technique of connecting different networks by using intermediary devices such as routers or gateway devices.
Internetworking ensures data communication among networks owned and operated by different entities using a common data communication and the Internet Routing Protocol. The Internet is the largest pool of networks geographically located throughout the world but these networks are interconnected using the same protocol stack, TCP/IP. Internetworking is only possible when the all the connected networks use the same protocol stack or communication methodologies.
Internetworking
A computer network is a set of different computers connected together using networking devices such as switches and hubs. To enable communication, each individual network node or segment is configured with similar protocol or communication logic, which usually is TCP/IP. When a network communicates with another network having the same or compatible communication procedures, it is known as Internetworking.
Internetworking is also implemented using internetworking devices such as routers.These are physical hardware devices which have the ability to connect different networks and ensure error free data communication. They are the core devices enabling internetworking and are the backbone behind the Internet.