The Transport layer is the layer-4 of the OSI reference model. The transport layer is mainly responsible for the process-to-process delivery of the entire message. A process is basically an application program that is running on the host.
The basic function of the Transport layer is to accept data from the layer above, split it up into smaller units, pass these data units to the Network layer, and ensure that all the pieces arrive correctly at the other end.
Furthermore, all this must be done efficiently and in a way that isolates the upper layers from the inevitable changes in the hardware technology.
The Transport layer also determines what type of service to provide to the Session layer, and, ultimately, to the users of the network. The most popular type of transport connection is an error-free point-to-point channel that delivers messages or bytes in the order in which they were sent.
The Transport layer is a true end-to-end layer, all the way from the source to the destination. In other words, a program on the source machine carries on a conversation with a similar program on the destination machine, using the message headers and control messages.
- The transport layer also identifies errors like damaged packets, lost packets, and duplication of packets, and provides sufficient techniques for error correction.
- The protocols of the network layer are only implemented in the end systems but not in the network routers.
- There are many services that are provided by the protocols of the Transport layer such as multiplexing, demultiplexing, reliable data transfer, the guarantee of bandwidth.
This layer mainly provides the transparent transfer of data between end-users, also provides the reliable transfer of data to the upper layers.
Figure: Transport Layer
Functions of Transport Layer
- Service Point Addressing: Transport Layer header includes service point address which is the port address. This layer gets the message to the correct process on the computer unlike Network Layer, which gets each packet to the correct computer.
- Segmentation and Reassembling: A message is divided into segments(that are transmittable); each segment contains a sequence number, which enables this layer in reassembling the message. The message is reassembled correctly upon arrival at the destination and replaces packets that were lost in transmission.
- Connection Control: It includes 2 types:
- Connectionless Transport Layer: Each segment is considered as an independent packet and delivered to the transport layer at the destination machine.
- Connection-Oriented Transport Layer: Before delivering packets, the connection is made with the transport layer at the destination machine.
- Flow Control: In this layer, flow control is performed end to end rather than across a single link.
- Error Control: Error Control is performed end to end in this layer to ensure that the complete message arrives at the receiving transport layer without any error. Error Correction is done through retransmission.
Let us now understand the process-to-process delivery by the transport layer.
Illustration of Process-to-Process Delivery

Thus the Transport layer is mainly responsible for the delivery of messages from one process to another.
connection management in transport layer
The connection is established in TCP using the three-way handshake as discussed earlier to create a connection. One side, say the server, passively stays for an incoming link by implementing the LISTEN and ACCEPT primitives, either determining a particular other side or nobody in particular.
The other side performs a connect primitive specifying the I/O port to which it wants to join. The maximum TCP segment size available, other options are optionally like some private data (example password).
The CONNECT primitive transmits a TCP segment with the SYN bit on and the ACK bit off and waits for a response.
The sequence of TCP segments sent in the typical case, as shown in the figure below −
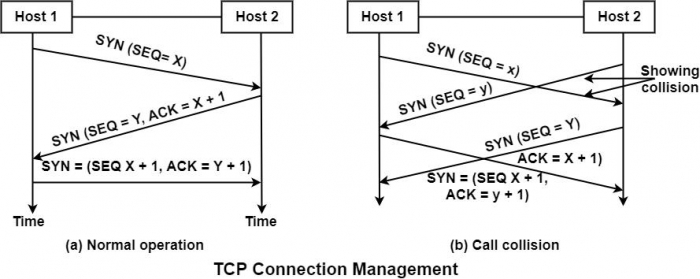
When the segment sent by Host-1 reaches the destination, i.e., host -2, the receiving server checks to see if there is a process that has done a LISTEN on the port given in the destination port field. If not, it sends a response with the RST bit on to refuse the connection. Otherwise, it governs the TCP segment to the listing process, which can accept or decline (for example, if it does not look similar to the client) the connection.
Call Collision
If two hosts try to establish a connection simultaneously between the same two sockets, then the events sequence is demonstrated in the figure under such circumstances. Only one connection is established. It cannot select both the links because their endpoints identify connections.
Suppose the first set up results in a connection identified by (x, y) and the second connection are also released up. In that case, only tail enter will be made, i.e., for (x, y) for the initial sequence number, a clock-based scheme is used, with a clock pulse coming after every 4 microseconds. For ensuring additional safety when a host crashes, it may not reboot for sec, which is the maximum packet lifetime. This is to make sure that no packets from previous connections are roaming around.
What is Session Layer?
The services provided by the first three layers are not enough for some processes. The session layer is also known as a network dialog controller, it creates, maintains, synchronizes the interaction between communicating applications.
- The session layer tracks the dialogs between systems, which are also called sessions. This layer manages a session by initiating the opening and closing of sessions between end-user application processes.
- It also controls single or multiple connections for each end-user application and directly communicates with both the presentation and the transport layers. The services provided by the session layer are generally implemented in the application environment using remote procedure calls (RPCs).
- In the Session layer, streams of data are marked and are resynchronized properly, so that the ends of the messages are not cut prematurely and data loss is avoided.
- A protocol such as Zone Information Protocol, AppleTalk Protocol, and Session Control Protocol are used to implement sessions on Web browsers.
- Through checkpointing and recovery session management and restoration are possible using these protocols.
- For example, in live television programs sessions are implemented, in which the audio and video streams emerging from two different sources are merged. This can be avoid overlapping and silent broadcast time.
This figure shows the relationship of the Session layer to the transport layer and presentation layer,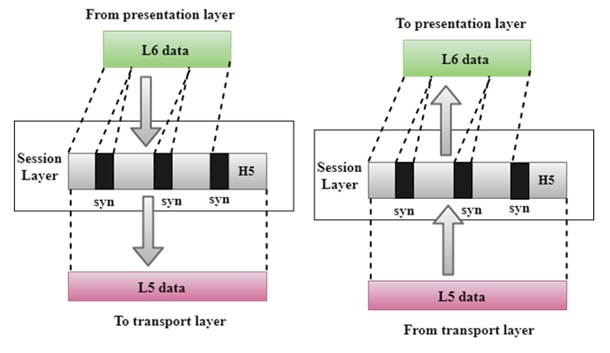
Session Layer
Design Issues with Session Layer
- Management of dialog control.
- It allows machines to make sessions between them seamlessly.
- Token management and Synchronization, such services also provided by the session layer.
- Provide quality and intensified services to the user.
Functionalities of session layer
Specific functionalities of the session layer are as follows:
1. Dialog Control
- The session layer behaves as a dialog controller.
- It allows two communication machines to enter into a dialog.
- It permits to communicate in either half-duplex (one way at a time) or full-duplex (two ways at a time) mode of communication.
- For Example, A dialog between a terminal connected to the mainframe can be half-duplex.
2. Synchronization
- This layer permitted a process to add checkpoints which are referred to as synchronization points into the stream of data.
- Example: If a system is sending a file of 2500 pages, It is advisable to add checkpoints after every 100 to ensures that a 100-page unit is successfully received and acknowledged independently.
- In this case, if a crash happens during transmission of page number 824; then retransmission begins on page 801. There is no need to retransmit pages 1 to 800 pages.
3. Token Management
This layer is also responsible for managing tokens. Through this, it prevents the two users to simultaneously attempt access of the same critical operation.
Presentation Layer
As we know, the OSI model layer has 7 layers and it is number 6 in layers. It is the layer between the application layer and the session layer and its function is to access all the information coming from the session layer.
After checking its accuracy, then after defining it well, all the information has to be presented to the application layer in its standardized format (standardized format).
When a machine sends any collected information to another machine, the syntax layer keeps in mind that the machine receiving all the information can understand the information and can also use all that information.
Meaning that the presentation layer plays the role of a translator or translator in the OSI model layer.

The presentation layer is also called the syntax layer, as its main function is to take care of the syntax and semantics of the information exchanged between any two communication systems. syntax means grammar and semantics mean semantics.
How A Presentation Layer Works
This layer works by converting all the information into a variety of file formats and forms of encryption.
The syntax layer is able to do these using built-in algorithms and is able to standardize the information whether it can be handled by XML, C++, or TLV.
In addition to passing all the information from the application layer to the session layer, the presentation layer is also responsible for passing information from the session layer to the application layer.
Functions of Presentation Layer
- Character-Code Translation
- Data Conversion
- Data Compression
- Data Encryption and Decryption
- Data Translation
- Graphic handling
Character-Code Translation –
It stores all the information given by the computer user in a different way, for example in some computers American standard code for information interchange (ASCII) code is used then in some computers Extended binary code decimal interchange code (EBCDIC) is used.
The syntax layer can translate ASCII into EBCDIC if needed.
Data Conversion –
It is responsible for changing the type of layer data for example it converts integer numbers to floating point numbers.
Data Compression –
It is able to compress the data by compressing it so that they can be transferred much faster.
Data Encryption and Decryption –
While transferring data in the network field, Data Encryption is required to keep all that information from hackers. Similarly, once the data reaches its destination user, there is a need to decryption it so that the usage of that data can be used.
The Presentation Layer facilitates data information encryption and decryption so that the user can be protected from hackers.
Data Translation –
We can connect different types of computers, laptops, mobiles, tablets, printers, screeners, servers and mainframes etc. using the network. All these computers use different types of Programming Language, Operating System and Language.
In such a situation, when one computer sends any information to another computer, then the data sent by it can be understood by another machine, so it is very important that the information of both computers is presented in the correct language to its destination computer.
The presentation layer acts as a translator that presents information to machines in understandable language.
Graphic handling –
It also presents various types of graphic such as images, videos etc. in an understandable format.
Protocols Supported at Presentation
- Independent Computing Architecture (ICA)
- Apple Filing Protocol (AFP)
- NetWare Core Protocol
- Network Data Representation
Independent Computing Architecture (ICA) –
The Independent Computing Architecture is a designed protocol for syntax server systems.
Network Data Representation –
It makes it understandable by correcting the syntax or grammar of the information received through the network.
Apple Filing Protocol (AFP) –
We are used to exchange data files of computers.
NetWare Core Protocol –
It was created by a company named Novell Inc, which uses it in its client-server operating system
Application Layer
The application layer sits at Layer 7, the top of the Open Systems Interconnection (OSI) communications model. It ensures an application can effectively communicate with other applications on different computer systems and networks.
The application layer is not an application. Instead, it is a component within an application that controls the communication method to other devices. It is an abstraction layer service that masks the rest of the application from the transmission process.
The application layer relies on all the layers below it to complete its process. At this stage, the data or the application is presented in a visual form that the user can understand.
Functions of the application layer
The application layer handles the following functions:
- ensures that the receiving device is identified, reachable and ready to accept data;
- when appropriate, enables authentication between devices for an extra layer of network security;
- makes sure necessary communication interfaces exist, such as whether there is an Ethernet or Wi-Fi interface in the sender’s computer;
- ensures agreement at both ends on error recovery procedures, data integrity and privacy;
- determines protocol and data syntax rules at the application level; and
- presents the data on the receiving end to the user application.
Two types of software provide access to the network within the application layer:
- network-aware applications, such as email; and
- application-level services, such as file transfer or print spooling.
